Enterprise Security Fundamentals
Rp500,000 Rp0
- Description
- Unit Outline
- Instructor
- Additional information
- Certificate
- Reviews (0)
Description
About this course
According to the Wall Street Journal, “All IT Jobs Are Cybersecurity Jobs Now.”
In this course, we examine the concept of Red team – Blue team security professionals. You will practice Red team versus Blue team exercises, where one group of security pros–the red team–attacks some part or parts of a company’s security infrastructure, and an opposing group–the blue team–defends against the attack. Both teams work to strengthen a company’s defenses.
You’ll learn how both the red and blue teams help the business attain a higher level of security, something the security industry is now calling the Purple team.
What you’ll learn
After completing this course, students will be able to:
- Describe the current enterprise security landscape
- Define the Assume Compromise approach
- Practice Red team versus Blue team exercises
- Develop organizational security preparation, processes, and responses
Prerequisites
There are no prerequisites for this course
Estimate Time : 8-16 hours
Module 1 Understanding the Cybersecurity Landscape
- Current Cybersecurity Landscape
- Assume Compromise Philosophy
- Cost of Breach
- Lab
Module 2 Red Team Penetration, Lateral Movement,Escalation, and Exfiltration
- Red Team Vs Blue Team Exercise
- The Attackers Objective
- Red Team Kill Chain
- Document Vulnerabilities
- Lab
Module 3 Blue Team Detection, Investigation, Response, and Mitigation
- Blue Team Kill Chain
- Restrict Privilege Escalation
- Restrict Lateral Movement
- Attack Detection
- Lab
Module 4 Beyond the Breach
- CIA Triad
- Organization Preparations
- Developing and Maintaining Policies
- Lab

Orin Thomas
Microsoft Cloud/Datacenter Specialist. Author. Microsoft MVP & Regional Director. Technical Raconteur.
Microsoft
Orin Thomas is an MVP, a Microsoft Regional Director, an MCT, and has a string of Microsoft MCSE and MCITP certifications. He has written more than 3 dozen books for Microsoft Press on topics including Windows Server, Windows Client, Azure, System Center, Exchange Server, Security, and SQL Server. He is an author at PluralSight and is a candidate in the Doctor of Information Technology program at Charles Sturt University.
Additional information
| Author / Publisher | Microsoft |
|---|---|
| Level | Beginner, Intermediate |
| Language | English |
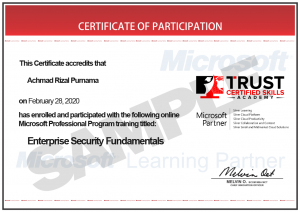
Certificate
Only logged in customers who have purchased this product may leave a review.
















Reviews
There are no reviews yet.